- Web Hosting
Host Zero - Affordable Hosting
Enjoy shared hosting at incredibly low prices with existing domain.
Free Domain Simplified Hosting
Hosting packages with *free domain, designed for all beginner needs.
Free .PK Domain Hosting
Fast, Reliable SSD Hosting with biannual billing & PK Domain.
Free .Ae Domain Hosting
Hassle-free bundle package for your business.
Advance Business Hosting
Fast, Secure plans with multiple backup facilities and virus scanner.
ASP.NET Hosting with Free Domain
Windows-based Plesk panel hosting plan. With SQL Server & Crystal Reports.
Hybrid Cloud VM
Dedicated Core Scalable at any Level with Unleashing Speed & Performance.
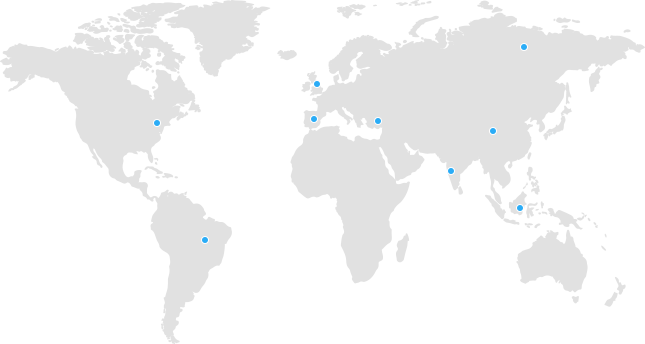
PK Dedicated Server
Fully customized Dell & Hp bare metal servers’ deployment in Pakistan.
International Dedicated Server
Intel & AMD, Latest Generation Server Readily Available for Enterprise Solutions.
- Domains
View All Domains
A domain name, signifies your own address on the Internet. As no two parties may ever hold the same domain name at the same time, it is a truly unique identifier of you or your company.Search Your Domain
Please enter your domain.Please verify that you are not a robot. - Development
Crafting top-tier web applications, providing user-friendly, optimized web development services for diverse global business modules. Experience highly secure web development solutions at a nominal cost
Crafting top-tier web applications, providing user-friendly, optimized web development services for diverse global business modules. Experience highly secure web development solutions at a nominal cost
Mobile app development involves the creation of software applications designed to operate and be utilized on mobile devices, including mobile phones and tablet computers.
Web Solutions
Crafting quality web solutions worldwide - secure, user-friendly, and cost-effective.
Mobile App Solutions
Your Go-To Partner for seamless Mobile App Development on Android and iOS platforms
- Solutions
- SSL
- Web Security
- NNGMS Packages
- OX App Suite
- G Suite
- Office 365 Plans
- SIEM/SOC Deployment
- Code Review & Analysis
- Security Audit
Website Security
SSL
Cutting-Edge SSL Solutions
Firewall
Fortifying Your Future
Malware Scanner
Digital Frontier Against Malicious Threats
Email
NNGMS
Budget-Friendly Solutions for Startups
OX App Suite
Robust email and productivity
G Suite
For small companies
Office 365
Comprehensive Office Solutions
Advanced Security
SIEM/SOC Deployment
SIEM/SOC Excellence
Code Review & Analysis
Empowering Your Software's Resilience
Security Audit
Security Audits for Cyber Protection
- About Us